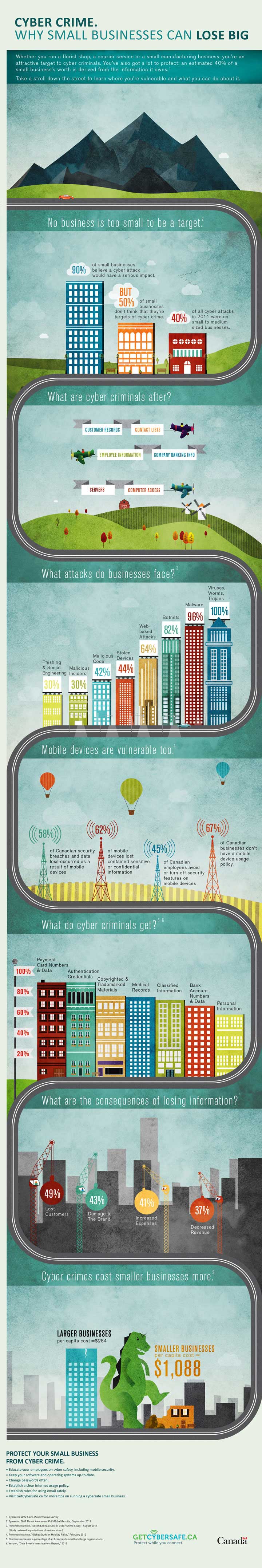
 When reading about cyber security, and big data breaches in the news these days, it's easy to think that these breaches only happen to big companies in another country. The reality is that no matter the size or scope of the breach, we are all at more risk that ever. And even worse, most of the time, cyber attacks are caused by or even executed by someone INSIDE the company that was attacked.
When reading about cyber security, and big data breaches in the news these days, it's easy to think that these breaches only happen to big companies in another country. The reality is that no matter the size or scope of the breach, we are all at more risk that ever. And even worse, most of the time, cyber attacks are caused by or even executed by someone INSIDE the company that was attacked.
In the 2016 Cyber Security Intelligence Index, IBM found that 60% of all attacks were carried out by insiders. Of these attacks, three quarters involved malicious intent, and one-quarter involved unintentional acts.
IBM research also found that health care, manufacturing and financial services are the top 3 industries under attack. Cyber attackers are drawn to the large amounts of personal data these companies store, their intellectual and physical property as well as their massive financial assets. All industries are at risk however. While industries and sectors differ in the value and volume of their assets – they all have one thing in common – People – all whom have the potential to be an insider threat.
- We-re only human – Human error is a major factor in breaches. From misaddressed emails to stolen devices to confidential data sent to unsecure home systems, mistakes can be costly. The riskiest of these are well-meaning IT admins whose complete access to company infrastructure can turn a small mistake into a catastrophe.
- A few people leak the passwords – Malicious employees whose intent is to steal or damage are a very real risk. Some steal competitive information, some sell data or intelligence, and some just have a vendetta against the organization.
- A wolf in Johns clothing from accounting – Cyber criminals are experts at hijacking identities. Some accomplish this by compromising an employee system through malware or phishing attacks; some leverage stolen credentials, especially by taking data from social networks. In some cases attackers can increase a hacked user’s access within a system, leading to even more sensitive information being compromised.
Based on the success of these types of attacks – they are often looked at as the perfect crime. Identifying these rogue elements can be so difficult in some organizations that they have gone to has resorted to “zero trust” environments. Security teams have another formidable adversary – REALITY. While restrictive policies may seem to be a valid strategy, they impede productivity, hamper innovation and frustrate users.
How to Minimize the Risk from Inside the Company
Be aware of what to look for and how to focus your security efforts:
- Focus on the right assets – Identify the most-valuable systems and data, and then give them the strongest defenses and the most frequent monitoring.
- Apply deep analytics – Humans are creatures of habit – they come to work at the same time and do familiar habits – the same can be said for how they use technology.
- Know your people – Understanding the users who hold the potential for the greatest damage is critical. Monitor IT admins, top execs, key vendors, and at-risk employees with greater vigilance.
- Don’t forget the basics – In security we love the newest tools – but getting the basics done well can make the biggest impact on insiders. Train your people, test them, and then try to trick them with fake exercises.
Next time you read a headline about some breach by an external hacker, remember that these attacks account for less than half of the breaches out there. And remember that the hacker probably used the identity of an unsuspecting employee to pull it off.
TAKE ACTION TO MAKE SURE YOUR ORGANIZATION ISN'T THE NEXT ONE MAKING HEADLINES. And in case your company or your system are eventually compromised, be sure that your disaster recovery program includes a strong cyber insurance policy. Protect your business with Armour. Sign up for Armour Cyber Insurance today.